Web developers have the incredibly difficult task of making sure the websites they create are safe. Not just for those who will be using them, but also for the client or company they work for. Every business with an online presence knows they need to prioritize security for their website and other online assets like intranet and apps. In our today’s learning, we will learn all about Internet Bot.
Many are starting to realize just how big a role bot detection plays in website security. Crawler bots have been a part of the internet for a very long time, and they’re not all bad. However, a huge chunk of today’s internet traffic is now made up of bad bots. These malicious bots are getting harder to track every year but are responsible for some of the most serious security threats.
Here’s a look at how bot technology has advanced, why it’s become so hard to detect them, and what steps can be taken to secure online assets against malicious bots.
What is an Internet Bot?
Bots have become a popular topic among those concerned with online security, so many people are familiar with them. But for anyone who’s still a bit in the dark, here’s a brief description:
Internet bots, also known as crawlers, can perform automated tasks with little human input. They typically perform simple tasks much faster than humans can. The latest iteration of bots can complete much more complex tasks as well.
Bots are employed for a wide variety of jobs, for instance, search engines like Google use bots to crawl and index websites.
Why are Internet Bot Potentially Dangerous?
Some cybercriminals use bots to complete tasks that they would typically have to do manually.
Since they can go on working automatically in the background, these bots can target a large group of websites in different ways without the hacker having to constantly oversee them.
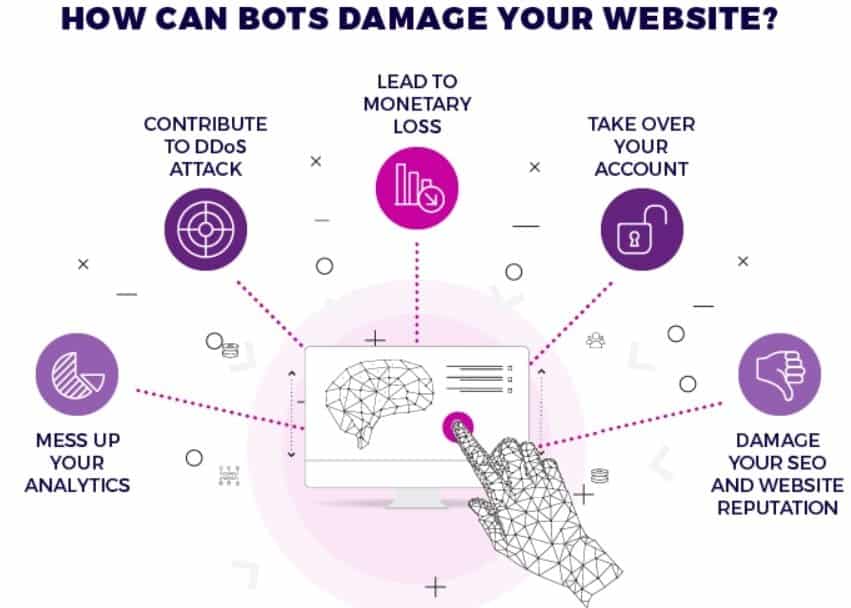
Malicious bots are effectively a type of malware that comes in many forms. They can infect websites, imitate visitors/users, steal information, execute DDOS attacks, spread spam, duplicate websites, etc.
How to Detect Malicious Internet Bot
Before, bots were easy to detect through fingerprinting and challenge tests. But this technology is advancing at an accelerated pace, making bots almost indistinguishable from human visitors. Their behavior is extremely convincing, which has led to the need for even more cutting-edge bot detection tools and methods.
These are a few of the more prominent bot detection tools out there.
Passive and Active Fingerprinting
While bots are becoming increasingly difficult to detect, building a bot capable of being indistinguishable from humans is complex. So complex, that many criminals often just don’t bother with it. Especially because it’s still lucrative to keep using less sophisticated bots. So it’s still lucrative to invest in both active and passive fingerprinting.
Attackers will undoubtedly use sophisticated bots to try and duplicate browsers and human behavior as much as possible. But that’s why it’s essential to dive deep and look at various indicators to cover all the bases. This includes looking at metrics, metadata, page load times, and using device fingerprinting.
Suspicious Traffic of Internet Bot
 It’s still possible to spot bots through suspicious traffic and unusual behavior. This isn’t just limited to IP-based threat detection. Yes, a surge in visits from locations that the website doesn’t usually cater to is a big red flag. But attackers have become smarter than that.
It’s still possible to spot bots through suspicious traffic and unusual behavior. This isn’t just limited to IP-based threat detection. Yes, a surge in visits from locations that the website doesn’t usually cater to is a big red flag. But attackers have become smarter than that.
Another relevant traffic metric is the number of direct visits. Bots don’t typically enter via sources like social media or referrals. Therefore, a surge in direct traffic should be investigated.
Real-Time Behavior Analysis
IP-based filtering has become fairly unreliable due to IoT hijacking and attackers using Tor for anonymity and shared IPs. This propels the need for better tools and technical applications to detect them.
Behavioral analysis is already playing a major role in bot detection and will continue to do so, as AI use becomes more widespread. Internet Bot detection will rely on real-time session tracking in conjunction with statistical analysis and server-side fingerprinting. Behavioral signals like touch and click events, and mouse movements, should be monitored as well.
Proper Device and Network Security Helps
Bot detection is only half the battle. Website developers/admins still need to be proactive about taking other security measures regarding their website, and their devices and network as well. This includes standard security practices like server security, device encryption, and keeping software and plugins up to date. It can also include network encryption through VPNs – which is something that many people tend to overlook.
For those still out of the loop, a virtual private network (VPN) sends network connection through an encrypted tunnel. It travels through a VPN server first, which masks the network’s IP address. The result is that attackers can’t track the user’s IP or succeed in SSL-based attacks.
Conclusion
No one has the luxury of time to detect bots manually anymore. Malicious internet bots have become highly sophisticated, and this calls from an equally complex response. It’s up to website developers (in partnership with admins) to secure their online and digital assets using advanced tools and detection methods.






Great article, totally what I was looking for.|