Cloud Internet Security is the trend of the present discussion. Many big and small organizations are spending huge money on Security. Data is the most valuable and vital asset of any business. That’s why people focus a lot on mitigating the menace of phishing through Internet Security.
Business owners spend a lot of time as well as money on their data security. This system is also a concern for IT managers and MIS officers. If data is on the cloud, then the terms “Internet Security” become very crucial. This article will discuss the Security issue of cloud internet. The ways of phishing, preventive measure, and the best possible solution and a cloud solution provider.
What is Cloud Internet Security?
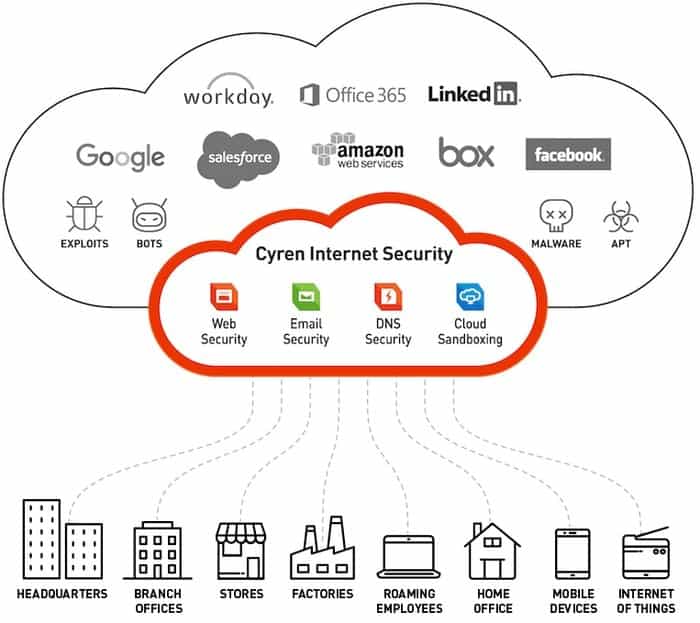
Security of Cloud Internet or, more simply, cloud security refers to a broad set of technologies, policies, and controls deployed to guard data, applications, and the associated setup of cloud computing. It is a sub-domain of internet security, network security, and information security.

Cloud allows storing data by the third party on cloud storage. An organization uses different services like PaaS, SaaS, and IaaS. They also use private, public and hybrid cloud storage. Different types of cloud operating systems transmit data. They make their system strong to protect data. For this, they use the password.
When the user stores data on public cloud storage, it becomes unable to access it directly. They use a remote access mechanism to use all applications. As a result, there raises a question of security.
Cloud security alliance reports that insider attacks are the six biggest threats in cloud computing. Therefore cloud service providers must ensure physical access to the online data server.
Cloud Internet Security Controls
An effective security system should realize all possible threats. It will be effective if the correct defective measure will take. After realizing the threats we can find four cloud security controls:
1. Preventive Controls
Preventive controls support the system against incidents, generally by plummeting if not removing weaknesses. Robust authentication of cloud users makes it less likely that unapproved users can access cloud storage systems and more likely that cloud users are recognized.
2. Detective Controls
Detective controls are planned to distinguish and answer correctly to any incidents that occur. In an attack, a detective control will signal the corrective or preventative controls to address the issue.
System and network security checking, including interference detection and hindrance arrangements, are typically employed to identify attacks on cloud systems and the supporting communications setup.
3. Corrective Controls
Corrective controls lessen the consequences of an incident. This control comes into consequence during or after an incident. However, an example is restoring system backups to rebuild a compromised system.
Recommended Post: 20 Tips You Need To Follow Before Choosing Any Cloud Web Hosting Service.
Top Cloud Internet Security Threats
There are lots of cloud security threats. A few will discuss in this article:
1. Data Breaches
Data breaches may be the first objective of cyber-attack. It may also occur for human error, poor security practice, and application vulnerabilities. These threats contain any data that was not planned for public release.
The peril of data breach is not exceptional to cloud computing. An establishment’s cloud-based data may have worth to different parties for different aims. As a result, it includes personally identifiable information, personal health information, financial information, trade secrets, and intellectual property. It steadily ranks as top anxiety for cloud customers.
2. Insufficient Identity, Credential, and Access Management
Bad actors can delete, modify or damage data. As a result, inadequate identity, credentials, or critical management can allow illegal access to data. It will be potentially devastating damage to establishments or end-users.
3. Insecure Interfaces and Application Programming Interfaces (APIs)
The cloud service provider offers user API. The customers use that API. Sometimes security depends on API. So API needs to design with proper attention.
4. System Vulnerabilities
By system vulnerabilities, wrong persons get access to the application. They take control of the database. As a result, threats arise on this issue. The various organization shares its storage and fall in the security problem.
5. Account Hijacking
In cloud computing, account hijacking is not new. When the attacker has access to users’ accounts, they will quickly get access to the systems. As a result, data will be manipulated. This account hijacking is now the base of attackers. So it is a critical area for a cloud user. It would be best if you considered this for cloud internet security.
6. Malicious Insiders
Inside users are also threads if they access it from outside. There should have an audit trail. Everything should be visible on the audit trail.
7. Advanced Persistent Threats (APTs)
APT is a parasitic form of cyber-attack. It intrudes on systems to establish a foothold in the IT infrastructure. APTs can transfer horizontally through data center networks and blend in with regular network traffic.
8. Data Loss of Cloud Services
Data may be lost for different reasons. Manipulation of data by the wrong person is a security issue as resulting integrity of data loss.
9. The Insufficient Due Diligence of Cloud Services
It is the duty to see the due diligence of IT manager or business professionals. Cloud service providers should guide the user in this aspect.
10. Denial of Service of Cloud Services
DoS attacks are designed to prevent users of a service from being capable of accessing applications. By obliging the cloud service to consumers excessive amounts of finite system resources such as disk space, processor power, memory, or network bandwidth, attackers can cause a system slowdown.
11. Shared Vulnerabilities of Cloud Services
Using software as a service may be a security issue. It is used by a different user as a shared service. As a result, security may hamper.
Final Thought
The most common problem or security issue is now data phishing. Users are now in the trap of data phishing. They got caught by email, social media, or mobile clone service. However, the user must be safe from security issues. All of those problems can be solved by cloud internet security.





